SHA-256 Hash Generator
Generate military-grade SHA-256 hashes locally using rapid Web Crypto APIs. Features HMAC-SHA256 mode and salting.
Tech Specs & Security
What is the SHA-256 Hash Generator?
SHA-256 Hash Generator is a high-performance, security-focused utility designed to compute 256-bit cryptographic signatures for any text or file. As part of the SHA-2 family, SHA-256 is the global standard for modern security, used in everything from SSL certificates to the Bitcoin blockchain. Unlike other tools that rely on external servers or heavy libraries, SHA-256 Hash Generator utilizes your browser's native 'SubtleCrypto' API. This access to hardware acceleration ensures military-grade security and near-native speeds. Because SHA-256 Hash Generator processes all data locally, your passwords, API keys, and private files remain entirely within your secure local environment.
Native Hardware Acceleration
Speed is critical when hashing large files or complex payloads. SHA-256 Hash Generator leverages the Web Crypto API to perform 'SubtleCrypto' digests directly on your machine's hardware. This eliminates the 'lag' associated with standard JavaScript hashing libraries. Whether you are generating a quick signature for a small string or computing a checksum for a 2GB ISO file, SHA-256 Hash Generator remains responsive and battery-efficient. For file integrity, SHA-256 Hash Generator uses a chunked reading approach, collecting data efficiently before producing a final uncrackable signature.
Pro Feature: HMAC & Salting
SHA-256 Hash Generator is built for advanced developer workflows. It includes a specialized HMAC-SHA256 mode, allowing you to generate Hash-based Message Authentication Codes for API integrations like AWS, Stripe, or webhooks. Additionally, SHA-256 Hash Generator features a specialized Salting toggle, where you can prepend or append a unique string to your input. This technique prevents 'Rainbow Table' attacks, ensuring that even common dictionary words produce unique, non-guessable hashes. This is the exact method used by professional authentication systems to secure user credentials.
Live Integrity Auditing
To ensure your data is actually secure, SHA-256 Hash Generator features a real-time Entropy Meter. This strength meter analyzes the complexity of your input string, warning you if your data is too simple to be secure—even after hashing. For system admins, SHA-256 Hash Generator also contains a Checksum Verifier. You can paste an expected SHA-256 hash from a software vendor, and SHA-256 Hash Generator will perform a case-insensitive match against your generated hash. A green 'Match' badge provides instant confirmation that your file is authentic and hasn't been corrupted during transfer.
How to Use the SHA-256 Hash Generator
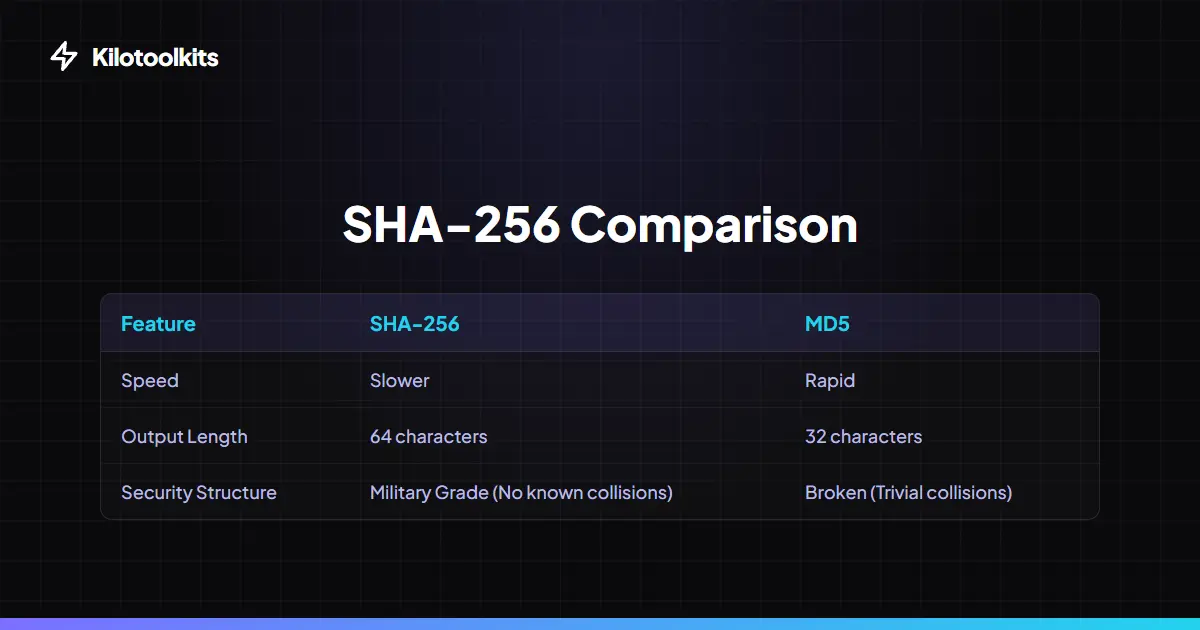
SHA-256 vs. Other Hashing Standards
| Metric | SHA-256 (This Tool) | SHA-1 | MD5 |
|---|---|---|---|
| Security Level | High (Current Standard) | Low (Legacy) | Broken |
| Output Length | 64 Hex Characters | 40 Hex Characters | 32 Hex Characters |
| Collision Probability | Virtually Zero | Proven Vulnerable | Extremely High |
| Best Use Case | Encryption / API Security | Legacy Systems | Checksums Only |
| Processing Speed | Hardware Accelerated | Fast | Ultra-Fast |
Hashing Security Limitations
While SHA-256 is an incredibly secure function, it is not a magic solution for poor input security. SHA-256 Hash Generator will warn you if your input is a 'weak string' like 'password123'. Always use a high-entropy string or a Salt string to prevent pre-computed dictionary attacks. If SHA-256 Hash Generator shows an error during file reading, check that the file hasn't been moved or deleted after dropping it. Since the Web Crypto API requires a secure context, SHA-256 Hash Generator will only function on HTTPS-enabled browsers to guarantee end-to-end local privacy.
Frequently Asked Questions
Tool Layout Gallery
Swipe to view more layouts